Developer’s Guide: Choosing the Right 2FA for Your App
- 6 days ago
- 3 min read
As a developer, implementing Two-Factor Authentication (2FA) is no longer a luxury—it’s a standard. But the "best" method isn't always the most secure one; it’s the one your users will actually use.

Here is how to weigh SMS-based OTP against Time-based One-Time Passwords (TOTP).
1. SMS-based OTP: The Low-Friction Entry
SMS sends a numeric code to a user’s phone via the cellular network.
When to use it:
Onboarding & Identity Verification: If your app is phone-number centric (like WhatsApp or a delivery app), SMS is the most seamless way to verify ownership of that "identity."
Low-Tech Demographics: If your user base isn't tech-savvy, asking them to download a secondary app (like Google Authenticator) might lead to high churn. Everyone knows how to read a text.
Account Recovery: It serves as a decent "Plan B" if a user loses their primary 2FA device.
The Developer's Trade-off:
Pros: Zero setup for the user; high adoption.
Cons: SIM Swapping and SS7 interceptions make it vulnerable to targeted attacks. It’s also expensive—you’ll pay per-message via providers like Twilio or Vonage.
2. TOTP: The Security Standard
TOTP uses a shared secret key (exchanged via QR code) to generate a code locally on the user's device every 30 seconds.
When to use it:
High-Value Accounts: If your app handles fintech, crypto, healthcare, or sensitive B2B data, TOTP should be the default recommendation.
Security-Conscious Users: Developers and tech enthusiasts expect TOTP support.
Global Apps: SMS delivery can be flaky in certain countries or restricted by local carriers. TOTP works offline, anywhere in the world.
The Developer's Trade-off:
Pros: Virtually free to implement (no per-message costs); immune to SIM swapping.
Cons: Higher friction. Users must download an app, and if they lose their phone without backup codes, they are locked out—meaning you have to build a robust account recovery flow.
Decision Matrix: Which should you implement?
Use Case | Recommended Method | Why? |
B2B / SaaS Admin Panels | TOTP | High risk; admins are usually tech-literate. |
Consumer E-commerce | SMS | Prioritizes conversion and ease of use. |
Banking / Fintech | Both (Tiered) | SMS for low-value; TOTP for high-value transfers. |
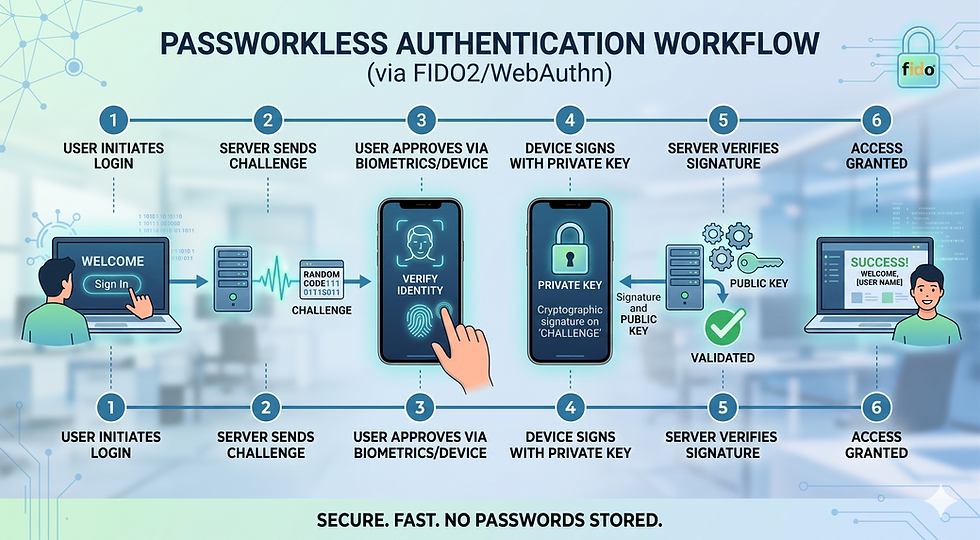
Developer Tools | TOTP / WebAuthn | Your users demand high security. |
Implementation Best Practices
If you use SMS:
Rate Limit Everything: Prevent attackers from using your API to spam numbers (and draining your wallet).
Short Validity: Set the OTP to expire in 2–5 minutes.
Sender ID: Use a consistent "Alpha Sender ID" so the message looks official.
If you use TOTP:
Provide Backup Codes: Generate a set of one-time "recovery codes" and force the user to confirm they’ve saved them.
Use Proven Libraries: Don't roll your own crypto. Use libraries like speakeasy (Node.js), pyotp (Python), or otplib.
QR Code Safety: Ensure the shared secret is stored encrypted in your database.
Final Verdict: The "Hybrid" Approach
For most modern apps, the best strategy is optionality.
Offer SMS as the default for ease of use, but provide a "Security Settings" menu where power users can upgrade to TOTP. This satisfies both the casual user who wants speed and the security-conscious user who wants protection.
NOTE: When you build applications using the Wizergos Low Code Platform, you can enable 2-factor authentication and SMS vs Time Based OTP just by checking a checkbox. All the heavy lifting of implementing the secure workflows are already built-in. As an application developer, all you need to do is understand your users and pick the right solution.



Comments